The operators behind the REvil ransomware group have resurfaced after allegedly closing shop following the widespread attack on Kaseya that caused thousands of victims on July 4.
Security researchers said all of the dark web sites for the prolific ransomware group — including the payment site, the group’s public site, the ‘helpdesk’ chat and their negotiation portal — went offline on July 13 after the Kaseya attack drew worldwide condemnation and tough threats from US lawmakers.
US President Joe Biden spoke personally with Russian President Vladmir Putin after the attack, and many attributed REvil’s closure to the conversation, where Biden pressed Putin about ransomware attacks originating from Russian soil.
Despite the conversation, both US authorities and Russian officials denied any involvement in REvil’s disappearance in July.
But dozens of security researchers took to social media on Tuesday to show that the group’s Happy Blog and other sites connected to REvil had resurfaced. Bleeping Computer reported that the newest entry was from a victim who was attacked on July 8.
Security researchers from Recorded Future and Emsisoft both confirmed that much of the group’s infrastructure was back online.
Ransomware expert Allan Liska told ZDNet that most people expected REvil to return, but with a different name and a new ransomware variant.
“Things definitely got hot for them for a while, so they needed to let law enforcement cool down. The problem (for them) is, if this is really the same group, using the same infrastructure they didn’t really buy themselves any distance from law enforcement or researchers, which is going to put them right back in the crosshairs of literally every law enforcement group in the world (except Russia’s),” Liska explained.
“I’ll also add that I’ve checked all of the usual code repositories, like VirusTotal and Malware Bazaar, and I have not seen any new samples posted yet. So, if they have launched any new ransomware attacks there haven’t been many of them.”
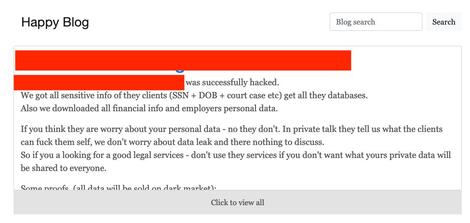
A screenshot of REvil’s Happy Blog.
Brett Callow
A report from security company BlackFog on ransomware attacks in August found that REvil accounted for more than 23% of the attacks they tracked last month. That was more than any other group tracked in the report.
REvil attacked at least 360 US-based organizations this year, according to Emsisoft threat analyst Brett Callow. The RansomWhere research site says the group has brought in more than $11 million this year, with high profile attacks on Acer, JBS, Quanta Computer and more.
REvil’s shut down in July left some victims in a tough spot. Mike Hamilton, former CISO of Seattle and now CISO of ransomware remediation firm Critical Insight, said one company paid a ransom after the Kaseya attack and received the decryption keys from REvil but found that they didn’t work.
REvil typically offered a help desk function that aids victims with getting back their data.
“Some of our customers got off really easily. If you had that agent installed on unimportant computers, you just rebuilt them and got back to life. But we got a distress call a few days ago from a company that got hit hard because they had a company that was managing a lot of their servers with the Kaseya VSA. They got a lot of their servers hit and had a lot of information on them and so they brought in their insurance company and decided to pay the ransom,” Hamilton said.
“They got their decryption key and when they started to use it, they found that in some places it worked and in other places it didn’t. These ransomware gangs have customer support but all of a sudden they went dark. They’re completely gone and so there is no help and these folks are just stuck. They’re going to end up losing a lot of data and they’re going to end up spending a lot of money to completely rebuild their network from scratch.”