The Trump administration is looking to develop a process that would have the federal government review the safety of powerful...
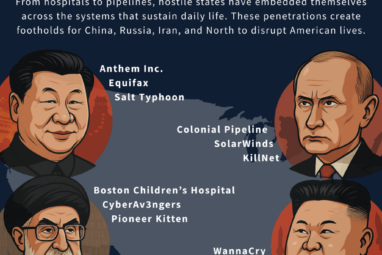
Michigan may be more than 6,000 miles away from the war in Iran, but, virtually speaking, it’s well within striking...
Before dawn on March 1, 2026, Iranian Shahed drones struck two Amazon Web Services data centers in the United Arab...
The darkness that swept over the Venezuelan capital in the predawn hours of Jan. 3, 2026, signaled a profound shift...
In the most talked-about film from the final year of the 20th century, “The Matrix,” a computer hacker named Neo...
Widely available artificial intelligence systems can be used to deliberately insert hard-to-detect security vulnerabilities into the code that defines computer...
As the United States experiences its latest government shutdown, most of the daily operations of the federal government have ground...
In the information age, multitasking is often worn as a badge of honor. But according to new research led by...
Scams are nothing new – fraud has existed as long as human greed. What changes are the tools. Scammers thrive...
We have developed a new way to secure video transmissions so even quantum computers in the future won’t be able...
The United States is trying to decouple its economy from rivals like China. Efforts toward this include policymakers raising tariffs...
Researchers at cybersecurity outlet Cybernews say that billions of login credentials have been leaked and compiled into datasets online, giving...