After disguising itself as a Windows 10 update earlier this month, the Emotet malware has now adopted a new template...
The Research Brief is a short take about interesting academic work. The big idea Game theory, which tries to predict...
A Hezbollah-affiliated threat actor known as Lebanese Cedar has been linked to intrusions at telco operators and internet service providers in the...
If you’re looking for a web hosting provider, you have a tremendous number of choices. In my Best web hosting...
Hackers were able to compromise the official campaign website of incumbent US President Donald Trump, which was briefly defaced this...
RISC-V, the emerging open-source instruction set processor architecture, is growing up. Sure, most of the attention has come from hardware...
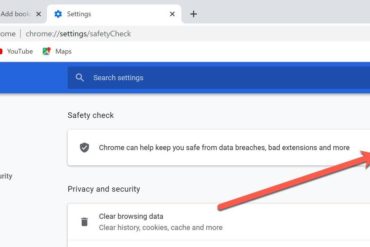
I know that a lot of you use Google Chrome. Despite its faults — I’m talking about how it devours...
A panel talk Friday afternoon brought together AI scholars Gary Marcus, Yoshua Bengio, Daniel Kahneman, Luis Lamb, and moderator Francesca...
The news about the Israel-Hamas war is filled with reports of Israeli families huddling in fear from relentless rocket attacks,...
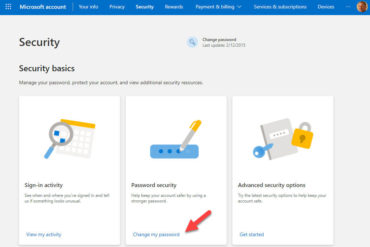
What’s your most valuable online account, the one most deserving of protection? If you use a Microsoft account to sign...
The European Commission recently proposed regulations to protect children by requiring tech companies to scan the content in their systems...
When a security vulnerability in the Cellmate chastity cage brought a new meaning to being locked up last year, you...