Security researchers have discovered this week a botnet operation that targets PostgreSQL databases to install a cryptocurrency miner. Codenamed by...
When Red Hat, CentOS‘s Linux parent company, announced it was “shifting focus from CentOS Linux, the rebuild of Red Hat...
Hackers are resetting passwords for admin accounts on WordPress sites using a zero-day vulnerability in a popular WordPress plugin installed...
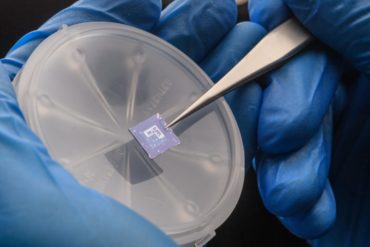
For decades, one material has so dominated the production of computer chips and transistors that the tech capital of the...
Security vulnerabilities in Point-of-sale (PoS) terminals produced by two of the biggest manufacturers of these devices in the world could...
Image via Alex Haney In a surprising and unexpected announcement on Thursday, the Facebook security team has revealed the real...
LONDON — Documents related to the development of the Pfizer-BioNTech Covid-19 vaccine have been “unlawfully accessed” in a cyberattack on...
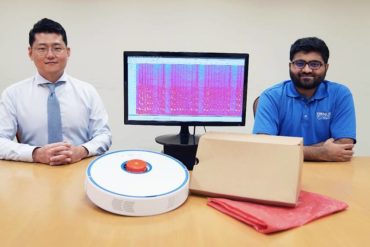
When your robot vacuum cleaner does its work around the house, beware that it could pick up private conversations along...
Researchers at a cybersecurity firm say they have identified vulnerabilities in software widely used by millions of connected devices—flaws that...
A hacker can reproduce a circuit on a chip by discovering what key transistors are doing in a circuit—but not...
QNAP has released a series of new patches which address both high and medium severity vulnerabilities in its NAS devices...
Image via PickPoint A mysterious hacker used a cyber-attack to force-open the doors of 2,732 package delivery lockers across Moscow....