A new strain of mobile ransomware abuses the mechanisms behind the “incoming call” notification and the “Home” button to lock screens on users’ devices.
Named AndroidOS/MalLocker.B, the ransomware is hidden inside Android apps offered for download on online forums and third-party websites.
Just like most Android ransomware strains, MalLocker.B doesn’t actually encrypt the victim’s files but merely prevents access to the rest of the phone.
Once installed, the ransomware takes over the phone’s screen and prevents the user from dismissing the ransom note — which is designed to look like a message from local law enforcement telling users they committed a crime and need to pay a fine.
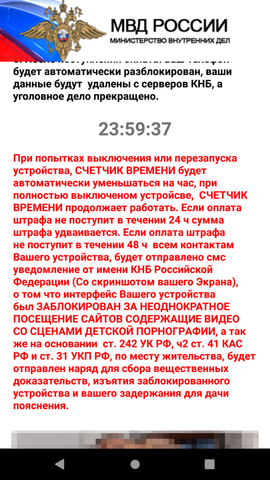
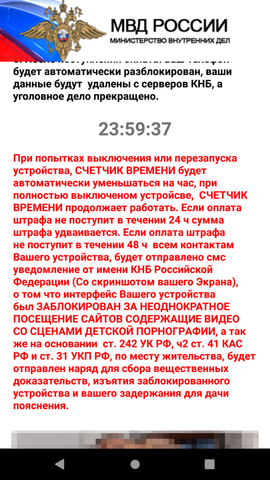
Ransomware posing as fake police fines has been the most popular form of Android ransomware for more than half a decade now.
Across time, these malware strains have abused various functions of the Android operating systems in order to keep users locked on their home screen.
Past techniques included abusing the System Alert window or disabling the functions that interface with the phone’s physical buttons.
MalLocker.B comes with a new variation of these techniques.
The ransomware uses a two-part mechanism to show its ransom note.
The first part abuses the “call” notification. This is the function that activates for incoming calls to show details about the caller, and MalLocker.B uses it to show a window that covers the entire area of the screen with details about the incoming call.
The second part abuses the “onUserLeaveHint()” function. This function is called when users want to push an app into the background and switch to a new app, and it triggers when pressing buttons like Home or Recents. MalLocker.B abuses this function to bring its ransom note back into the foreground and prevent the user from leaving the ransom note for the home screen or another app.
The abuse of these two functions is a new and never-before-seen trick, but ransomware that hijacks the Home button has been seen before.
For example, in 2017, ESET discovered an Android ransomware strain named DoubleLocker that abused the Accessibility service to re-activate itself after users pressed the Home button.
Since MalLocker.B contains code that is too simplistic and loud to make it past Play Store reviews, users are advised to avoid installing Android apps they downloaded from third-party locations such as forums, website ads, or unauthorized third-party app stores.
A technical breakdown of this new threat is available on Microsoft’s blog.



