A dispute broke out on Tuesday after cybersecurity company Rapid7 released a report about a vulnerability in a Fortinet product...
Fortinet has patched a vulnerability that attackers could have leveraged to take complete control of a device with the highest...
Cyberattacks on IoT devices have shown no signs of slowing as more and more vulnerabilities become known. While most of...
Colonial Pipeline sends breach letters to more than 5,000 after ransomware group accessed SSNs, more
Colonial Pipeline is sending out breach notification letters to 5,810 current and former employees whose personal information was accessed by...
T-Mobile said Monday it had begun an investigation after a hacker group claimed to have obtained data from some 100...
(image: WP Engine) If you’re looking for a web hosting provider, you have a tremendous number of choices. In my...
It’s now well known that usernames and passwords aren’t enough to securely access online services. A recent study highlighted more...
StackCommerce Don’t wait for New Year’s Day to start making major changes to your life when you can train at...
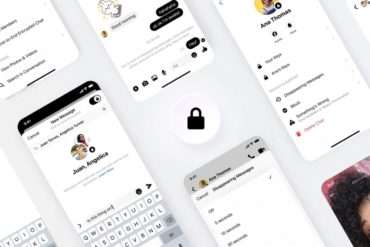
Voice and video calls on Facebook Messenger are getting more secure, with the option of end-to-end encryption now rolling out...
Cornell Tech researchers have discovered a new type of online attack that can manipulate natural-language modeling systems and evade any...
Nearly all of the $600 million stolen in one of the biggest cryptocurrency heists ever has now been returned by...
Microsoft has revealed the inner-workings of a phishing attack group’s techniques that uses a ‘jigsaw puzzle’ technique plus unusual features...