Smartwatches might be good for tracking steps and heart rates, but they can also offer hackers a wealth of personal...
EPFL researchers in computer and communication sciences are hacking and fixing Android phones before malicious hackers do. They uncovered 31...
From data breaches to widespread systemic shutdowns, cyberattacks like the 2024 Fulton County (Georgia) government attack now occur as regularly...
A research team led by faculty from Binghamton University, State University of New York has been exploring how mass layoffs...
Chatbots powered by artificial intelligence (AI) can pass a cybersecurity exam, but don’t rely on them for complete protection. That’s...
A team of researchers at the University of Texas at Arlington has developed software that prevents artificial intelligence (AI) chatbots...
As travelers rush to book their summer getaways, Booking.com’s internet safety boss says watch out for supercharged AI scams. Marnie...
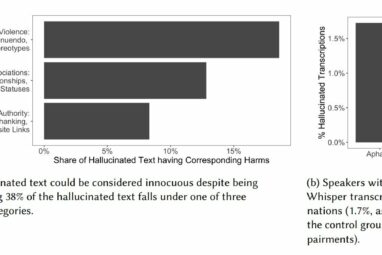
Speak a little too haltingly and with long pauses, and OpenAI’s speech-to-text transcriber might put harmful, violent words in your...
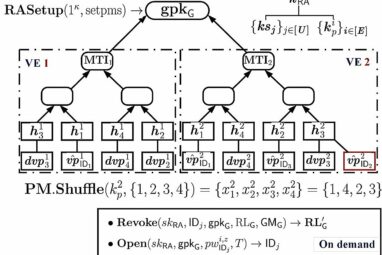
“Please enter the code within the next two minutes.” The concept of one-time passwords (OTPs) has become a mainstay in...
Researchers have collected and analyzed an unprecedented amount of data on SMS phishing attacks, shedding light on both the scope...
Leading AI scientists are calling for stronger action on AI risks from world leaders, warning that progress has been insufficient...
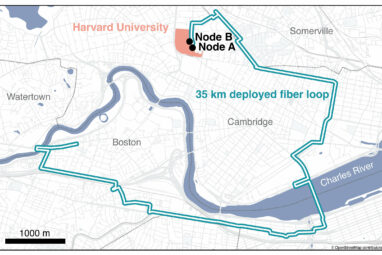
It’s one thing to dream up a quantum internet that could send hacker-proof information around the world via photons superimposed...