FiberHome HG6245D router
At least 28 backdoor accounts and several other vulnerabilities have been discovered in the firmware of a popular FTTH ONT router, widely deployed across South America and Southeast Asia.
FTTH ONT stands for Fiber-to-the-Home Optical Network Terminal. These are special devices fitted at the end of optical fiber cables. Their role is to convert optical signals sent via fiber optics cables into classic Ethernet or wireless (WiFi) connections.
FTTH ONT routers are usually installed in apartment buildings or inside the homes or businesses that opt for gigabit-type subscriptions.
A slew of hardcoded credentials
In a report published last week, security researcher Pierre Kim said he identified a large collection of security issues with FiberHome HG6245D and FiberHome RP2602, two FTTH ONT router models developed by Chinese company FiberHome Networks.
The report describes both positive and negative issues with the two router models and their firmware.
For example, the positive issues are that both devices do not expose their management panel via the IPv4 external interface, making attacks against its web panel impossible via the internet. Furthermore, the Telnet management feature, which is often abused by botnets, is also disabled by default.
However, Kim says that FiberHome engineers have apparently failed to activate these same protections for the routers’ IPv6 interface. Kim notes that the device firewall is only active on the IPv4 interface and not on IPv6, allowing threat actors direct access to all of the router’s internal services, as long as they know the IPv6 address to access the device.
Starting with this issue, Kim detailed a long list of backdoors and vulnerabilities he discovered on the device, which he claims attackers could abuse to take over ISP infrastructure. These issues include the likes of:
The management interface leaks device details if accessed from a browser with JavaScript disabled. One of the leaked details is the device’s MAC address.A backdoor mechanism allows an attacker to use the device’s MAC address to initiate a Telnet connection to the router by sending a specially crafted HTTPS request [https://[ip]/telnet?enable=0&key=calculated(BR0_MAC)].Passwords and authentication cookies for the admin panel are stored in cleartext in HTTP logs.The management interface is secured through a hardcoded SSL certificate stored on the device that can be downloaded and used for MitM and other attacks.The web server (management panel) includes a list of 22 hardcoded credentials, which Kim believes were added and in use by different internet service providers.
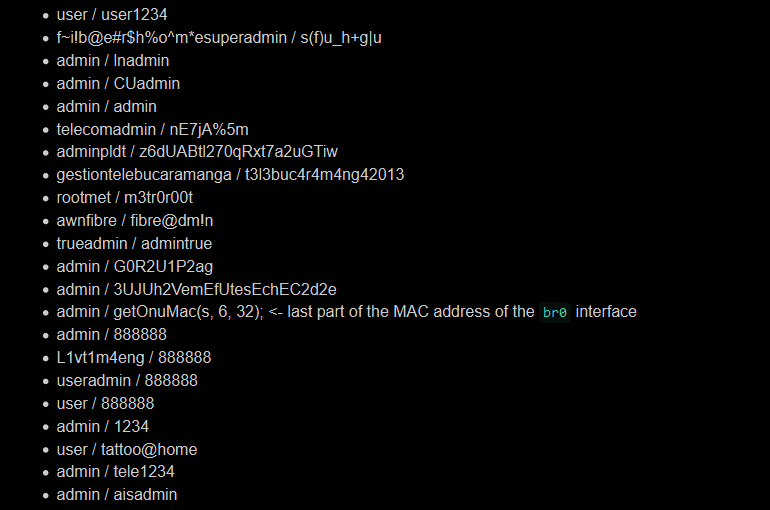
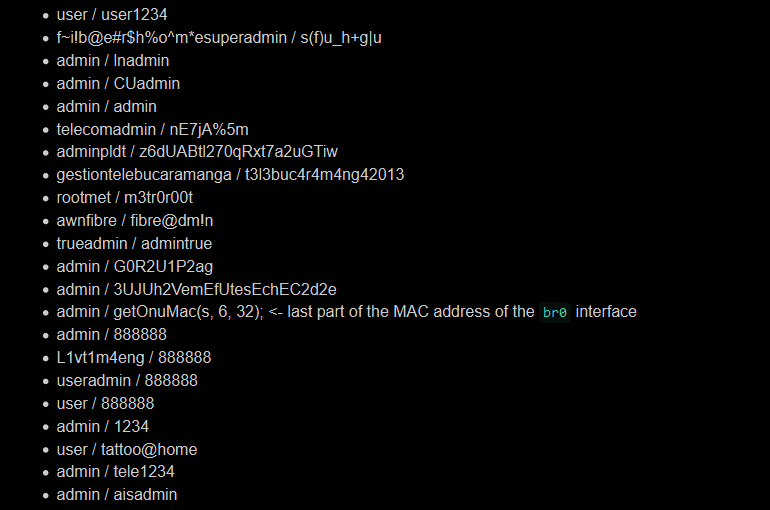
The firmware also includes hardcoded credentials for managing the device via the TR-069 protocol.There are also credentials in the web server binary that are encrypted. However, the XOR key to decrypt them is also in the binary, rendering their encryption useless. As Kim notes, this is the same XOR key used in the firmware of C-Data devices, also impacted by similar backdoor issues.A hardcoded root password for a Telnet server is also included. This server is disabled by default, though.The firmware also includes different sets of hardcoded credentials for a low-level Telnet account. Kim found four.A privilege escalation vulnerability in the Telnet daemon allows attackers to escalate their privileges to root level.But the Telnet authentication can also be bypassed entirely, via two different methods.Or you can use a denial of service bug to crash Telnet entirely.Furthermore, various passwords for other router services are stored in cleartext inside the firmware or the router’s NVRAM.
Based on the number and nature of the hardcoded backdoor accounts he discovered inside the device’s firmware, Kim said that he believes “that some backdoors have been intentionally placed by the vendor.”
Requests for comment sent by ZDNet to FiberHome via email and its official website last Thursday, January 14, remained unanswered at the time of writing.
Kim said he found these issues in January 2020 and had notified the vendor. The researcher couldn’t determine if any bugs have been patched as he hasn’t tested newer versions of the firmware since then.
Furthermore, the researcher also warns that the same backdoor/vulnerability issues could also affect other FiberHome models due to the fact that most vendors tend to reuse or slightly edit firmware between different production series.
FiberHome devices were abused last year
It is of utmost urgency that device owners secure FiberHome routers. In late 2019, security researchers from Qihoo 360 reported that threat actors had been already abusing FiberHome systems to assemble botnets, most used as proxy networks.
In May 2020, the US Department of Commerce added FiberHome and eight other Chinese tech companies to a blacklist restricting its access to US companies, exports, and technology.
In a press release, US officials claimed the nine companies were “complicit in human rights violations and abuses committed in China’s campaign of repression, mass arbitrary detention, forced labor and high-technology surveillance against Uighurs, ethnic Kazakhs, and other members of Muslim minority groups in the Xinjiang Uighur Autonomous Region (XUAR).”