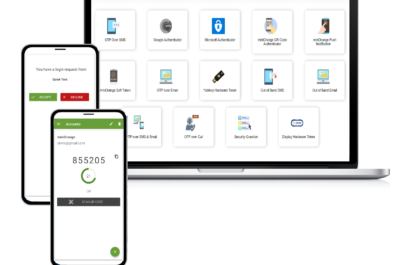
As an extra layer of security, several online services have adopted push notification-based two-factor authentication systems, whereby users must approve...
When you use the internet, you leave behind a trail of data, a set of digital footprints. These include your...
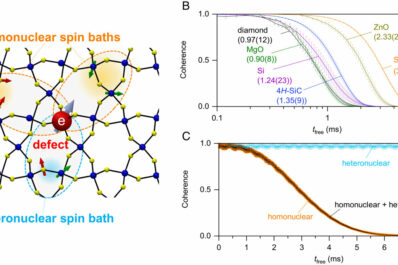
A new, elegant equation allows scientists to easily compute the quantum information lifetime of 12,000 different materials. Scientists have uncovered...
In 2014, as Russia launched a proxy war in Eastern Ukraine and annexed Crimea, and in the years that followed,...
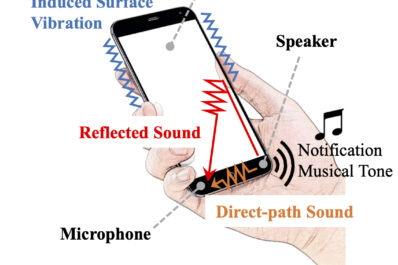
Could your smartphone be spying on you? Hopefully not, and if so, not for long, thanks to a team of...
Throughout the latter half of 2021, as it became clear that Russia was massing a large portion of its conventional...
President Joe Biden on March 21, 2022, warned that Russian cyberattacks on U.S. targets are likely, though the government has...
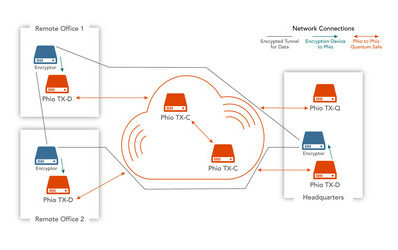
It’s fairly reasonable to assume that an encrypted email can’t be seen by prying eyes. That’s because in order to...
You’ve probably seen an infusion pump, even though the name might make it sound like a mysterious piece of medical...
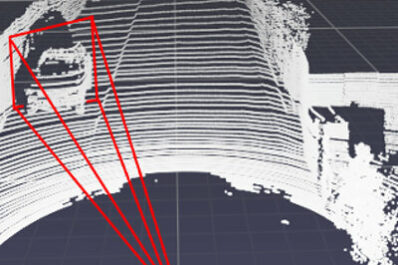
Researchers at Duke University have demonstrated the first attack strategy that can fool industry-standard autonomous vehicle sensors into believing nearby...
As smartphones have grown more sophisticated over the years, so too have their accompanying security measures. Simple passwords have been...
Engineers sometimes turn to nature for inspiration. Cold Spring Harbor Laboratory Associate Professor Saket Navlakha and research scientist Jonathan Suen...