Ransomware-as-a-Service (RaaS) ads on hacking forums
Image: ZDNet
Ransomware-as-a-Service is a cyber-security term referring to criminal gangs that rent ransomware to other groups, either via a dedicated portal or via threads on hacking forums.
RaaS portals work by providing a ready-made ransomware code to other gangs. These gangs, often called RaaS clients or affiliates, rent the ransomware code, customize it using options provided by the RaaS, and then deploy in real-world attacks via a method of their choosing.
These methods vary between RaaS affiliate and can include email spear-phishing attacks, en-masse indisciriminate email spam campaigns, the use of compromised RDP credentials to gain access to corporate networks, or the use of vulnerabilities in networking devices to gain access to internal enterprise networks.
Payments from these incidents, regardless of how the affiliates managed to infect a victim, go to the RaaS gang, who keeps a small percentage and then forwards the rest to the affiliate.
RaaS offerings have been around since 2017, and they have been widely adopted as they allow non-technical criminal gangs to spread ransomware without needing to know how to code and deal with advanced cryptography concepts.
The RaaS tiers
According to a report published today by Intel 471, there are currently around 25 RaaS offerings being advertised on the underground hacking scene.
While there are ransomware gangs who operate without renting their “product” to other groups, the number of RaaS portals available today far exceeds what many security experts thought could be available and shows the plethora of options that criminal gangs have at their disposal if they ever choose to dip their toes in the ransomware game.
But not all RaaS offerings provide the same features. Intel 471 says it’s been tracking these services across three different tiers, depending on the RaaS’ sophistication, features, and proven history.
Tier 1 is for the most well-known ransomware operations today. To be classified as a Tier 1 RaaS, these operations had to be around for months, proven the viability of their code through a large number of attacks, and continued to operate despite public exposure.
This tier includes the likes of REvil, Netwalker, DopplePaymer, Egregor (Maze), and Ryuk.
With the exception of Ryuk, all Tier 1 operators also run dedicated “leak sites” where they name-and-shame victims as part of their well-oiled extortion cartel.
These gangs also use a wide variety of intrusion vectors, each depending on the type of affiliates they recruit. They can breach networks by exploiting bugs in networking devices (by recruiting networking experts), they can drop their ransomware payload on systems already infected by other malware (by working with other malware cartels), or they can gain access to company networks via RDP connections (by working with brute-force botnet operators or sellers or compromised RDP credentials).
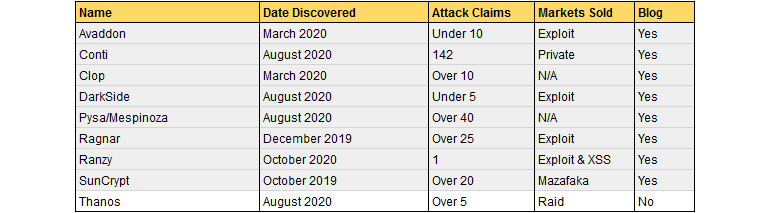
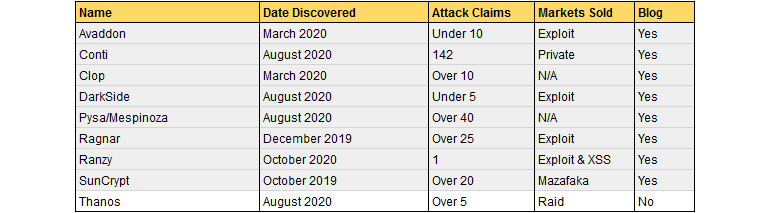
Tier 2 is for RaaS portals that have gained a reputation on the hacking underground, provide access to advanced ransomware strains, but have yet to reach the same number of affiliates and attacks as Tier 1 operators.
This list includes the likes of Avaddon, Conti, Clop, DarkSide, Mespinoza (Pysa), RagnarLocker, Ranzy (Ako), SunCrypt, and Thanos — and these are effectively the up-and-comers of the ransomware world.
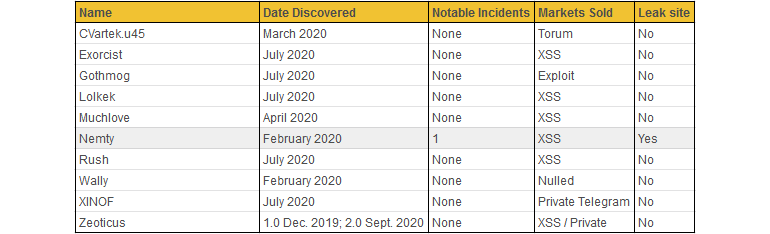
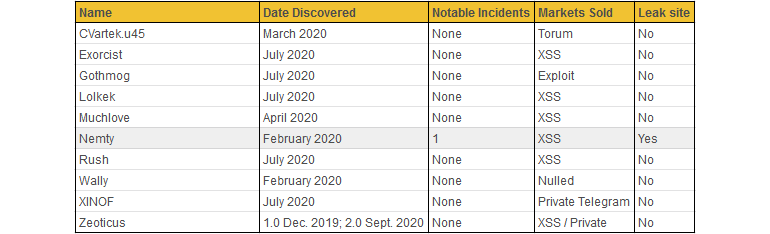
Tier 3 is for newly launched RaaS portals or for RaaS offerings about which there’s limited to no information available. In some cases, it is unclear if any of these are still up and running or if their authors gave up after trying and failing to get their portals off the ground.
This list currently includes the likes of CVartek.u45, Exorcist, Gothmog, Lolkek, Muchlove, Nemty, Rush, Wally, Xinof, Zeoticus, and (late arrival) ZagreuS.
All in all, while the underground cybercrime ecosystem is generating profits through criminal activity, it is still a market, and, just like all markets, it is governed by the same principles that guide any other market today.
A large number of service providers is the tell-tale sign of a booming economy that is far from being saturated. Saturating the RaaS market will only happen when criminals create more RaaS portals than affiliate groups are willing to sign up for or when companies bolster their security measures, making intrusion harder to carry out, drying up profits for crooks.


